Android Malware in the Wild
The Guardian reports that two instances of malware for Android phones have been reported in the wild. This matters because it means that cellphone malware is moving from proof-of-concept to actual danger.
One pretends to be a movie application and sends text messages to sites which charge a premium. The charges then show up on your phone bill. Similar applications were common in the Windows PC environment during the dial-up days.
The software is not available in the Android market place and seems to be most common in Russia. Creepily enough, warns users of what might happen at time of install. From the Guardian article:
Prior to installation, as required by Android’s application permissions, the “Media Player” asks users to confirm permission for the application to run “services that cost you money (send SMS messages)”.
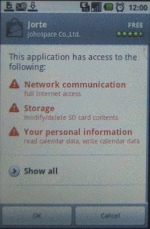
The Android software installation routine includes a warning about what types of information a piece of software needs to access; the picture shows a sample warning window.
The moral of this is that reading is good.
The other is a flaw in earlier versions of the Android web browser when it is used for a compromised website or on an unsecured wireless network; it has been fixed in more recent versions. Like many browser flaws, it allows back door access; also, like many browser flaws, the danger is probably more theoretical than real.
And this is why I think that: I doubt that bad guys are sitting around in coffee bars trying to break into random phones using the wireless hotspots. Even if a phone has Wi-Fi capability, many folks don’t use it routinely. If someone tries to exploit this vulnerability, I expect the target of the attack has been selected in advance.
This does not mean the vulnerability should not have been fixed. As persons keep more and more personal information, including financial information, on their phones, the chances of attack increase. Nevertheless, I don’t think the average Android user should be losing sleep over this . . . yet.


